Server as Shield
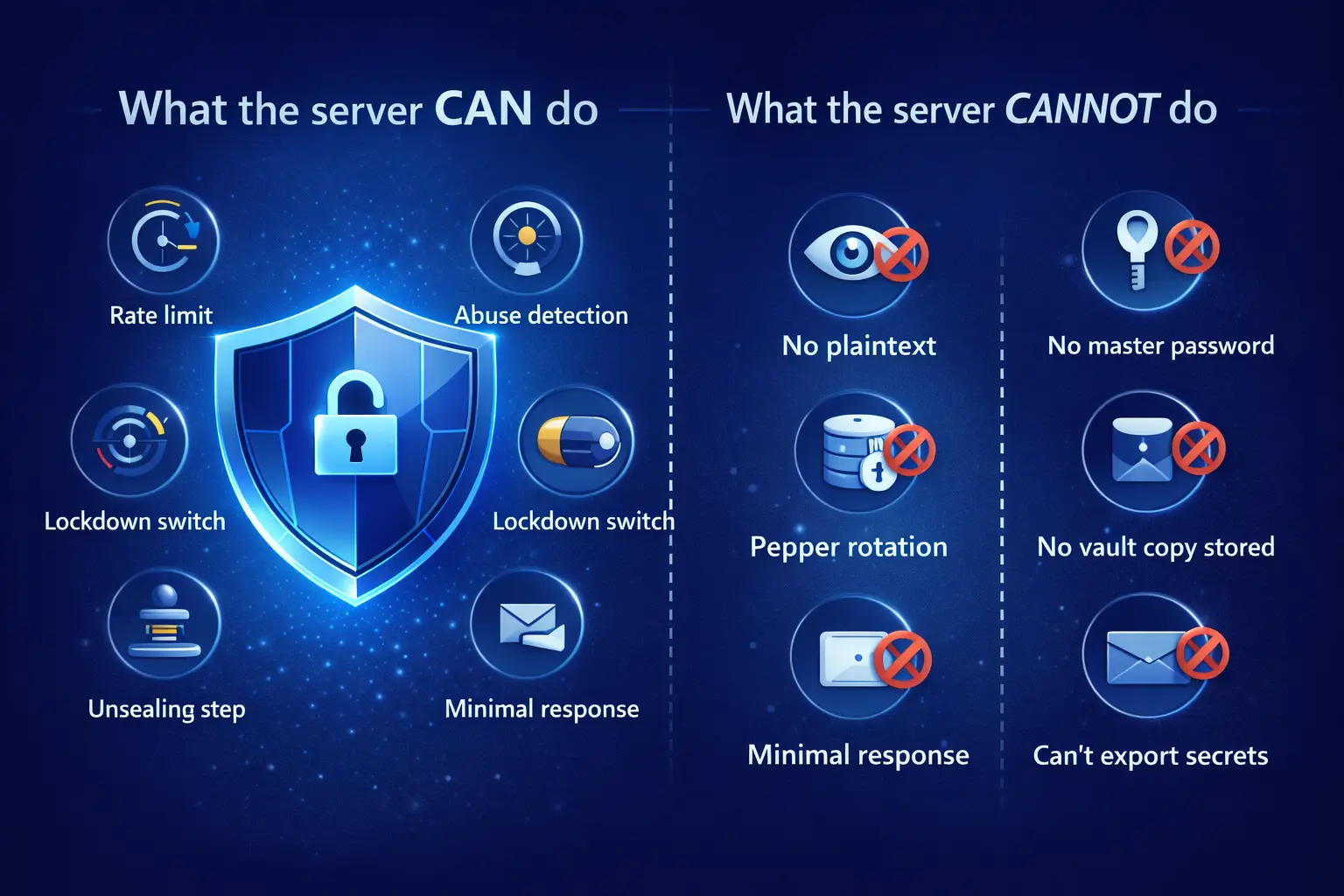
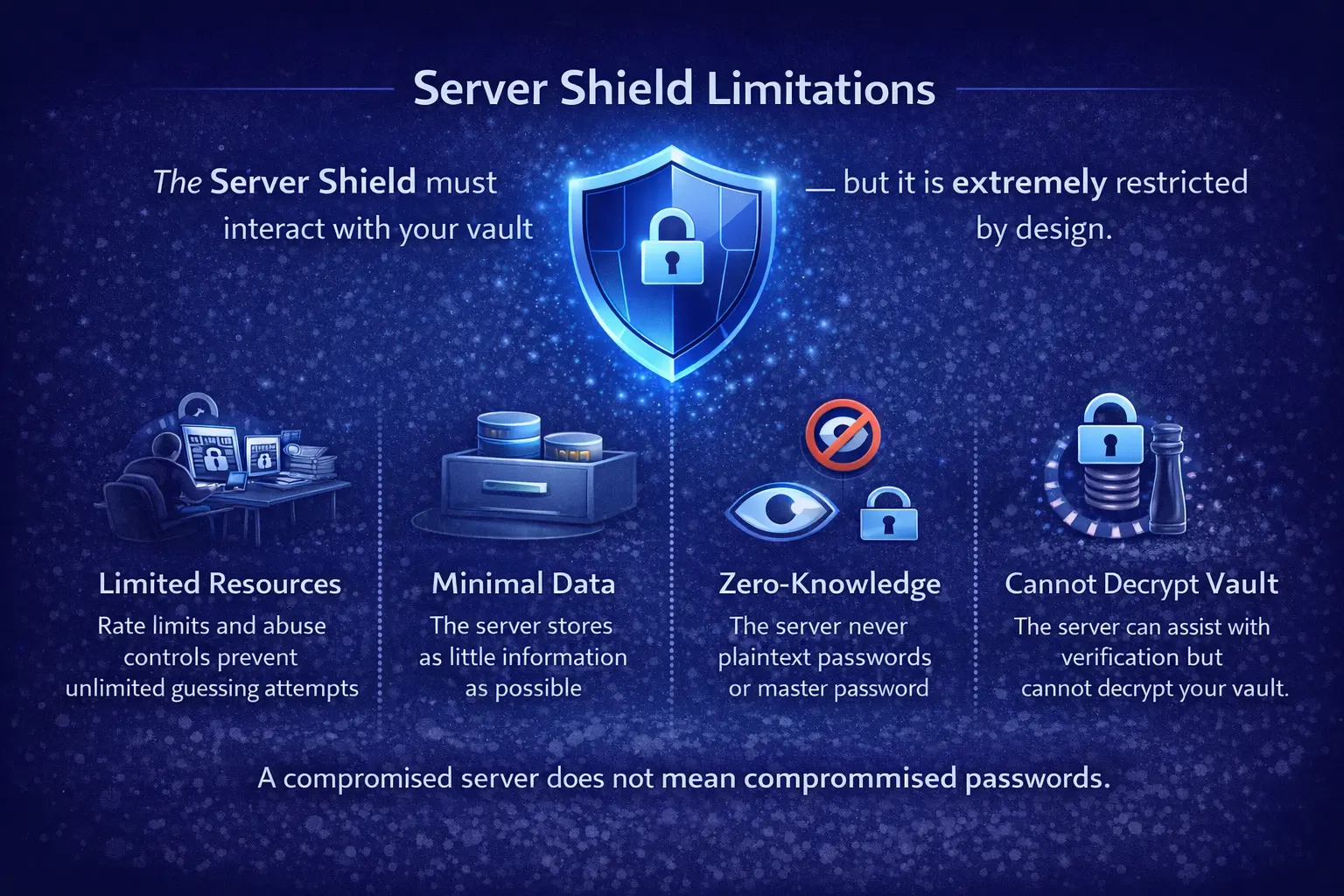
WQR uses the server as a security layer - not as vault storage.
WQR uses the server as a security layer - not as a place to store your vault.
Most password managers pick one of two extremes:
- Offline-only unlocking: great independence and privacy, but if someone steals/copies your vault files, they can try passwords offline at full speed.
- Cloud vault storage: convenient sync, but you're trusting a cloud vault database (a big target) with a copy of your encrypted vault.
WQR takes a different approach:
- Your vault stays on your device (stored as encrypted WQR code files).
- Unlocking is protected online (server-gated), so large-scale offline brute-force is blocked.
- Plaintext never leaves your device.
This design is about one thing: reducing risk when things go wrong (stolen files, copied backups, malware trying offline guesses) without turning your vault into "someone else's stored data".